Inbound Rules
Configure inbound routing rules for decryption and signature verification.
When are inbound rules applied?
Inbound rules apply whenever a message is sent to your domain. They serve two central purposes:
- Decryption: Only authorized recipients can read the content of an encrypted message.
- Signature verification: The authenticity and integrity of the message are ensured.
Guide: Create an Inbound Rule
1. Create a New Route
- Open the "Routing" menu and click "+".
- In the first step, select "inbound".
2. Select Security Protocol
- Decide which protocols should be considered (multiple selection possible):
- S/MIME: Certificate-based decryption and signature verification
- PGP: Key-based decryption and signature verification
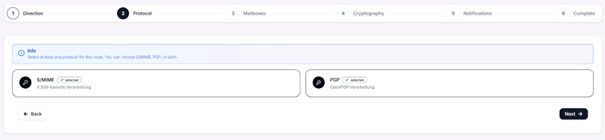
Tip: Details about the protocols can be found in the Cryptography section.
3. Define Sender and Recipient
- Determine which messages the rule applies to:
- Custom: Specific mailbox or wildcard (*).
- Group: Apply to a predefined group.
- All: Applies to all inbound messages.
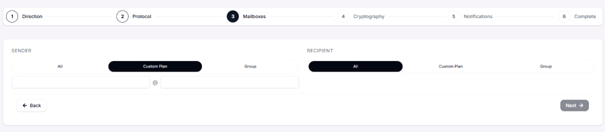
Note: If you have not yet created any groups, follow the guide in the Groups section.
4. Configure Cryptography Options
- Decryption: Do not decrypt / Decrypt if possible
- Signature verification: Do not verify / Verify if possible
- Keys:
- Use a specific certificate or key
- Automatic selection from available imports (default)
- Automatic import: Automatically saves incoming keys and certificates from communication partners.
- Remove signature: Removes the certificate after verification by Conbool.
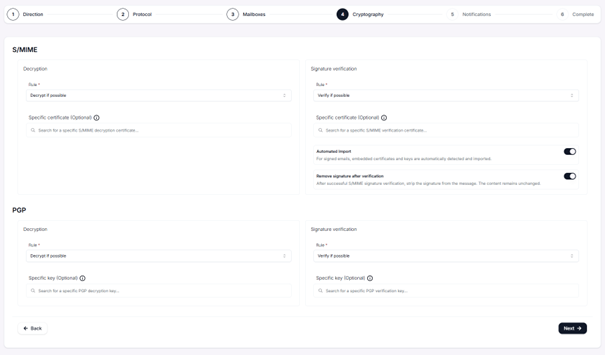
Tip: Make sure that the required certificates or keys have been imported beforehand.
5. Enable Notifications (optional)
- Display the cryptography status in the subject line of inbound messages, e.g.:
- Successful / failed decryption
- Successful / failed signature verification
6. Save Rule
- Review the settings in the summary.
- Click "+" to activate the rule. It will then appear in the overview.
Important Notes
- Inbound rules apply exclusively to messages addressed to your domain.
- Make sure that all required certificates or keys are stored in the "Cryptography" section.